Authorization in Django: From Permissions to Policies : Part 6 — Why Convention-Based Permissions Scale
Scaling Authorization by Freezing the Permission Boundary
By the time a system reaches any meaningful size, the question is no longer whether authorization exists, but where complexity is allowed to live.
Django’s permission system is deliberately narrow. It refuses context. It refuses state. It refuses to decide when something is allowed or why. It names capabilities and nothing more. This restraint often feels unsatisfying—especially to engineers familiar with expressive rule engines, policy DSLs, or attribute-driven authorization models.
And yet, Django’s approach scales unusually well.
This part explains why.
Not by arguing that rule engines are “bad,” but by showing why constraint, convention, and determinism outperform expressiveness at the permission layer of a real system.
Constraint as a Scaling Mechanism
Most authorization failures in large systems are not caused by missing features. They are caused by unexpected interactions.
Every additional axis of expressiveness—time, ownership, state, environment, role inheritance—multiplies the number of mental models required to reason about access. That multiplication does not remain local. It propagates into reviews, audits, migrations, incident response, and onboarding.
Django’s permissions system avoids this by construction.
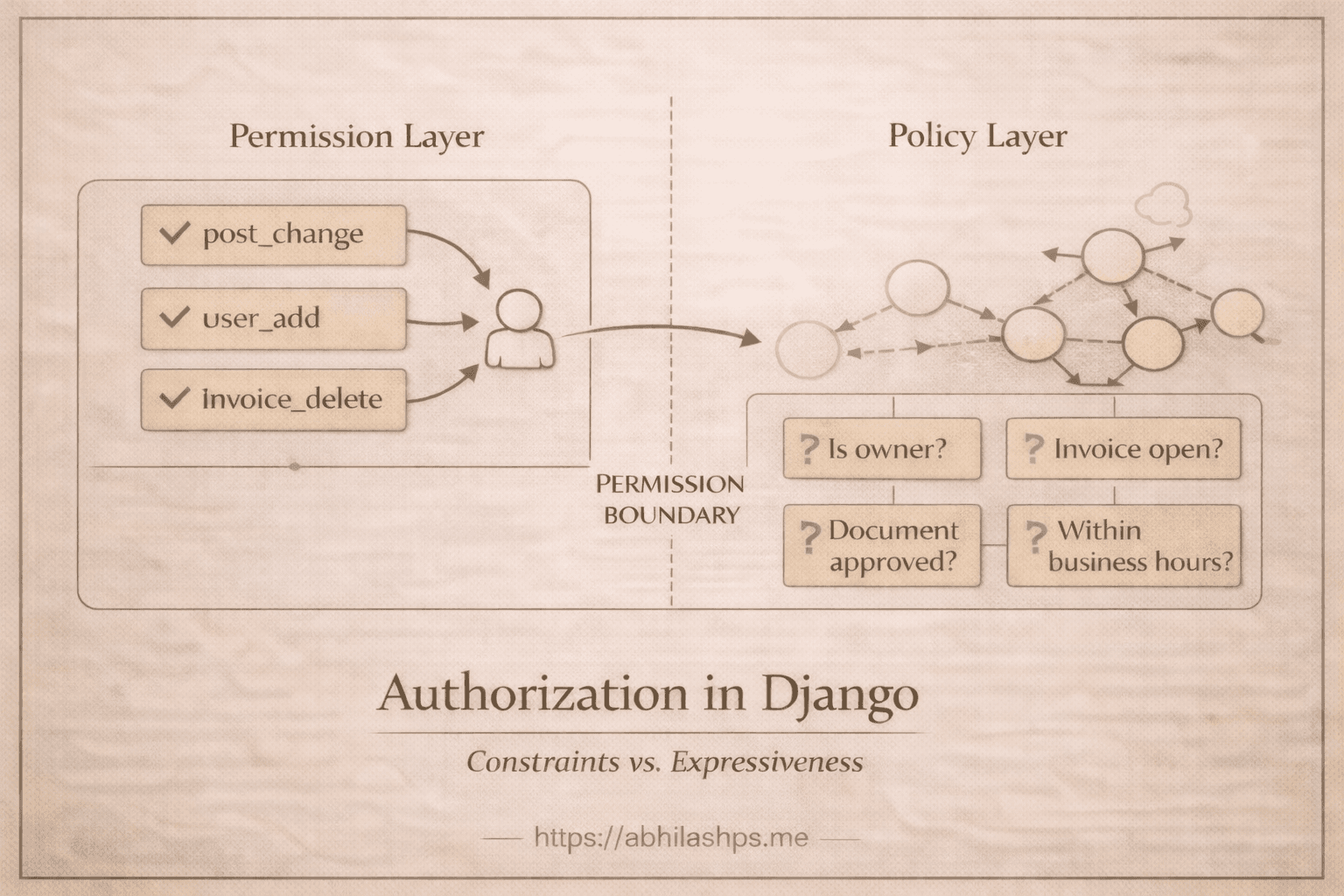
A permission answers only one question:
Is this actor allowed to attempt this class of operation on this class of object?
Nothing more.
This constraint collapses the problem space. There are no edge cases where permission evaluation depends on runtime state, request context, or historical data. The system cannot express those conditions—and therefore cannot fail in those ways.
Constraint, here, is not a limitation. It is a guardrail against accidental privilege expansion.
Convention Beats Configuration at Scale
Configuration works well in small systems because it feels clear and flexible. We can see the rules, adjust them, and shape them to fit local needs.
As systems grow, that flexibility turns into risk.
Every configurable permission model forces each consumer to understand how permissions were defined. Admin interfaces, serializers, audit tools, and internal dashboards must all interpret the same configuration in exactly the same way. Over time, they drift.
Django avoids this problem by not making permissions configurable.
Permissions are created by convention—one set per model, one name per action. Because the shape is fixed, every tool already knows what to expect. No discovery step is needed. No custom wiring is required.
That is why Django Admin works without setup.
That is why DRF can enforce permissions without configuration.
That is why audits can list permissions mechanically.
Convention creates a shared contract. That contract is what allows tools to scale without coupling.
Determinism Over Interpretation
Authorization systems fail quietly when their outcomes depend on interpretation.
Rule engines evaluate expressions. Expressions depend on data. Data changes. Evaluation paths branch. Over time, the same request can yield different authorization outcomes under slightly different conditions.
Django’s permission checks resolve to deterministic database queries.
No branching logic.
No evaluation order.
No side effects.
The system does not “decide” in the moment. It looks up.
This matters operationally. Deterministic checks are cacheable, indexable, debuggable, and observable. They behave predictably under load. They fail loudly when data is missing. They are fast because they are simple.
Performance is not an accident here. It is a consequence of refusing interpretation.
Stable Surface Area Enables Coordination
Surface area is everything other parts of the system are allowed to assume without asking.
Large systems are built by teams that do not move together or release at the same pace.
When authorization contracts change often—or change indirectly through logic updates—coordination breaks down. We are forced to track not only which permissions exist, but what they currently mean. That cost grows quickly as teams, services, and deployments multiply.
Django avoids this by freezing the permission surface area.
Permission codenames are stable identifiers. They are not derived at runtime. They are not recalculated. They do not change when logic changes. Once created, they persist as durable references that code, migrations, documentation, and audits can all depend on.
This stability lets plugins integrate safely.
It lets deployments upgrade independently.
It lets teams reason locally without re-checking global assumptions.
At that point, the permission layer stops being application logic. It becomes infrastructure.
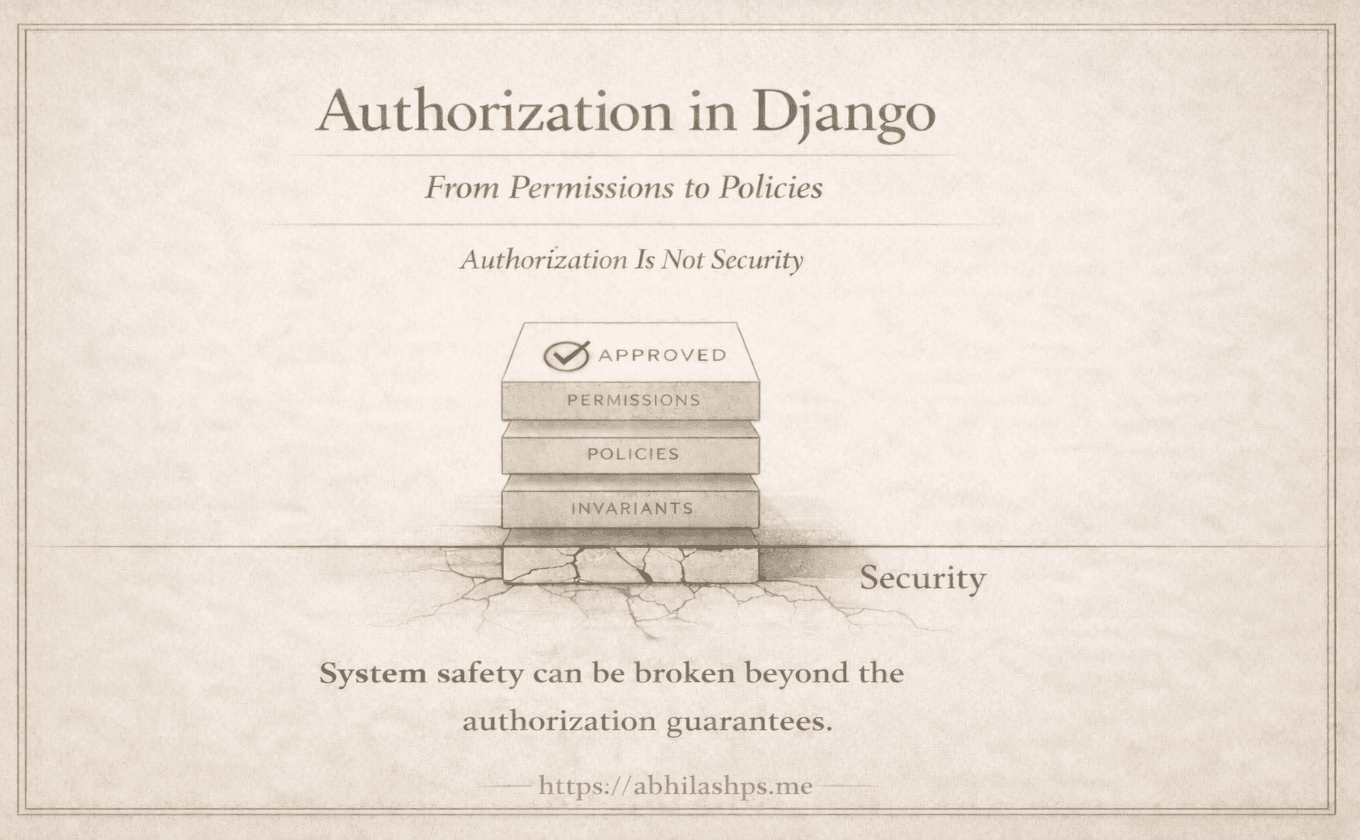
Why Rule Engines Fail at the Permission Layer
Rule engines are not inherently flawed. They are simply misplaced when embedded into permissions.
Rules introduce time (“only after approval”), state (“if the order is open”), and context (“unless the user is the owner”). These dimensions are real—but they are not properties of capability. They are properties of policy and invariants.
When rules are attached to permissions, two things happen:
The permission layer becomes temporal (means dependent on time or sequence) and unstable.
The boundary between authorization and domain logic dissolves.
This makes enforcement ambiguous. A permission no longer signals a clear contract; it signals a conditional promise whose meaning must be re-derived at runtime.
Django avoids this by refusing to host rules at all.
Authorization as Infrastructure, Not Logic
Permissions in Django are not a decision system. They are a coordination system.
They exist so that higher layers—policies, invariants, workflows—can assume a shared baseline of capability without re-litigating identity or intent. Likewise, they are deliberately shallow so that deeper logic can remain explicit, testable, and local to the domain.
This separation is what allows permissions to scale indefinitely while policies evolve.
The system remains boring. Predictable. Unexpressive. And safe.
Where We Go Next (Part 7 Preview)
By the end of this part, one conclusion should feel unavoidable:
Permissions must stop somewhere.
If they do not, they consume responsibilities that belong to state machines, invariants, and policy enforcement layers. Django draws that boundary early—before complexity can leak inward.
The next part examines what happens beyond that boundary.
In Part 7, we will look at the exact points where permissions fail—and why that failure is not a flaw, but a signal that a different architectural tool is required.